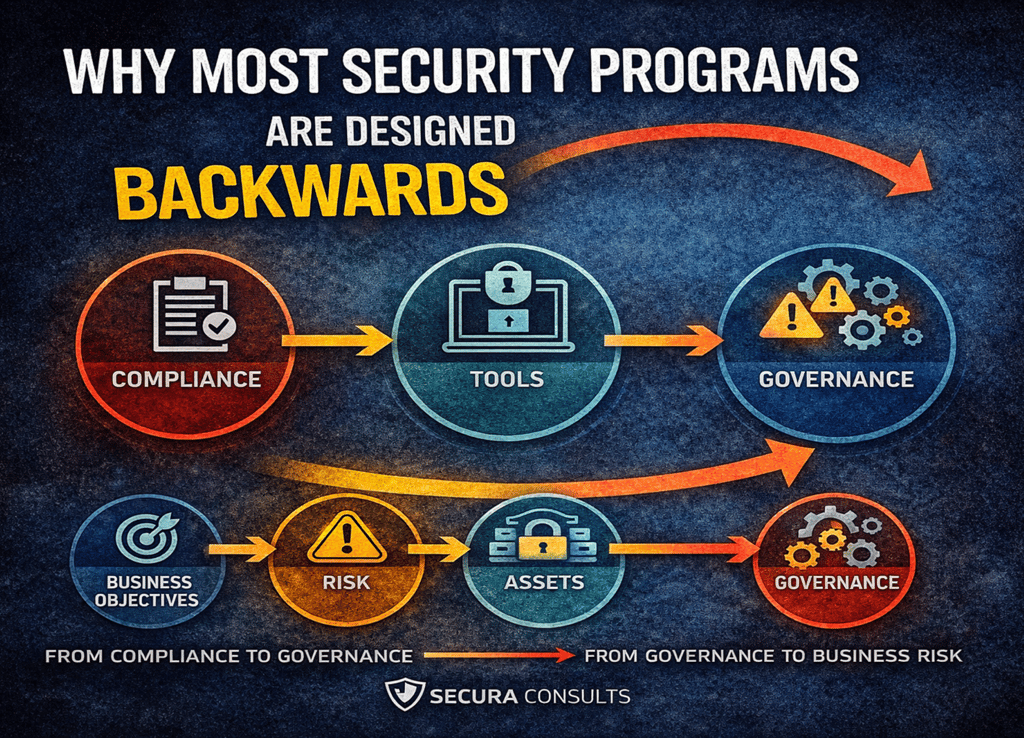
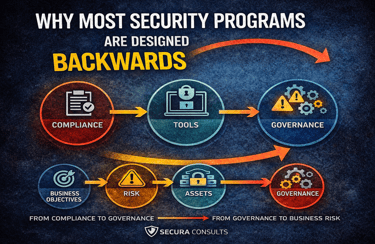
Why Most Security Programs Are Designed Backwards
Many security programs are built around tools, certifications, or regulatory checklists rather than risk architecture and governance clarity. This article examines why that sequence weakens long-term effectiveness and outlines a structured, risk-first approach to designing security programs that align with business objectives, asset criticality, and measurable control performance.
GOVERNANCE
Ugochukwu Ezeakuji
2/26/20264 min read
Security programs rarely fail because organizations do not care about security. They fail because they are designed in the wrong order.
In many organizations, security begins with urgency. A new regulation is introduced. A customer requests assurance documentation. A board member asks about cyber risk. A major breach appears in the news. In response, leadership allocates budget. Tools are purchased. Policies are drafted. Certifications are pursued.
From the outside, this appears proactive. In reality, many programs are built backwards.
Instead of beginning with risk architecture and governance clarity, they begin with controls and documentation. Instead of defining what must be protected and why, they focus on proving that something is in place. Instead of aligning security with business objectives, they align security with checklists.
The result is not necessarily non-compliance. It is something more subtle: a program that looks mature but lacks structural coherence.
The Tool-First Trap
A common starting point for security initiatives is tooling. An organization deploys:
Endpoint detection and response platforms
SIEM solutions
Cloud security posture management tools
Data loss prevention software
dentity and access management systems
These technologies are valuable. Many are necessary. But when introduced without a defined governance model, they operate in isolation. Tools cannot compensate for undefined risk appetite. They cannot replace asset prioritization. They cannot determine which exposures are tolerable and which are existential.
Without a clear understanding of business risk drivers, security tooling becomes reactive instrumentation — alerting on symptoms rather than enforcing strategy.
A mature program begins by asking:
What are our most critical assets?
What operational processes depend on them?
What regulatory or contractual exposures exist?
What level of disruption can the organization tolerate?
Only after these questions are answered does tool selection become strategic rather than opportunistic.
The Compliance-First Distortion
Another common misalignment is designing security around compliance frameworks rather than operational risk. Compliance is important. Regulatory alignment matters. Certifications may be necessary for market access. But compliance frameworks are external reference points. They are not substitutes for internal risk architecture.
When organizations design security programs primarily to “pass compliance audits,” several distortions occur:
Policies are written to satisfy clause requirements rather than operational realities.
Evidence collection becomes more important than control performance.
Risk assessments are conducted for documentation rather than decision-making.
Security ownership is delegated entirely to compliance teams.
This creates a fragile equilibrium.
On paper, the organization is compliant. In practice, security controls may not reflect evolving threats, business expansion, or technology changes. Compliance can initiate structure. It should not dictate architecture.
Governance Before Controls
An effective security program begins with governance clarity. Governance answers three foundational questions:
·Who is accountable for risk decisions?
· How is risk tolerance defined and approved?
· How are control effectiveness and residual risk reported to leadership?
Without explicit accountability structures, security becomes an IT function rather than an enterprise discipline. Without defined risk appetite, teams cannot prioritize effectively. Every issue appears urgent, or none do. Without reporting mechanisms that translate technical risk into business impact, executive oversight remains superficial.
Governance is not bureaucracy. It is decision architecture.
Only once governance structures are defined should organizations proceed to control design.
Asset-Centric Architecture
A security program designed correctly is anchored to asset criticality. Not all systems are equal. Not all data sets carry equivalent regulatory or reputational risk. Not all business processes require identical protection intensity.
An asset-centric approach involves:
Identifying “crown-jewel” assets
Mapping data flows across systems
Understanding dependencies between services
Assessing concentration risk
Evaluating third-party reliance
Controls are then layered proportionally.
High-impact systems receive stronger monitoring, stricter access governance, and more frequent review. Lower-risk environments are governed appropriately but efficiently. This approach avoids both over-engineering and under-protection.
Designing for Effectiveness, Not Existence
Security controls often exist in documentation but lack operational effectiveness.
Examples include:
· Access reviews conducted quarterly but without meaningful scrutiny
· Incident response plans documented but never exercised
· Vendor risk assessments completed at onboarding and never revisited
· Encryption standards declared but not consistently validated
A backward-designed program treats the existence of these controls as sufficient.
A forward-designed program asks:
How do we know this control works?
When was it last tested?
What evidence demonstrates performance?
What metrics indicate degradation?
Control effectiveness requires measurement. Measurement requires intent. Without this feedback loop, security stagnates.
Integration with Business Strategy
Security cannot be designed independently of business trajectory. It must be aligned with business strategy.
If an organization plans to:
Expand into new markets
Introduce AI-driven services
Migrate infrastructure to cloud-native architectures
Integrate with additional third-party APIs
Then security design must anticipate these shifts.
Programs designed backwards often retrofit controls after expansion, leading to fragmented governance. Programs designed forward incorporate scalability into their architecture. They assume growth, vendor proliferation, and technological evolution. Security maturity is not static compliance. It is adaptive governance.
The Role of Executive Oversight
When security is designed backwards, executive involvement is limited to approval of policies or acknowledgement of audit results.
When designed correctly, executives engage with:
Risk tolerance thresholds
Residual risk reporting
Incident scenario modeling
Resource allocation trade-offs
Control investment prioritization
Security becomes part of strategic decision-making, not just operational maintenance. Board-level discussions move beyond “Are we compliant?” to “What is our exposure and how are we managing it?” That shift fundamentally changes program design.
A Structured Forward Design Model
An effective security program typically progresses in this order:
Define business objectives and risk appetite
Identify critical assets and data flows
Assess threat landscape and exposure
Establish governance and accountability structures
Design control architecture aligned to risk
Select and deploy tools to enforce controls
Implement monitoring and measurement mechanisms
Conduct periodic reassessment and refinement
Reversing this sequence — beginning with tools or compliance checklists — leads to misalignment. The difference may not be immediately visible. But over time, structural weaknesses accumulate.
Security as Architecture, Not Reaction
Organizations that design security programs forward tend to exhibit certain characteristics:
Clear ownership of risk decisions
Defined escalation pathways
Measurable control performance indicators
Consistent access governance discipline
Active vendor oversight
Regular scenario testing
Their programs feel coherent. Organizations that design backwards often exhibit:
Redundant or overlapping tools
Confusion around accountability
Policies disconnected from practice
Audit fatigue
Reactive remediation cycles
The distinction is architectural, not cosmetic.
Moving from Backward to Forward
Redesigning a security program does not require abandoning existing investments. It requires reframing them.
Start by:
Re-evaluating asset criticality
Clarifying risk appetite at leadership level
Mapping controls to specific risk drivers
Eliminating redundant or low-impact activities
Establishing measurable effectiveness criteria
This transition transforms security from compliance artifact to operational discipline.
Conclusion
Most security programs are not ineffective because they lack effort. They are ineffective because they lack order. Designing security backwards — beginning with tools or certifications — may produce documentation and dashboards. It does not necessarily produce resilience.
Effective programs begin with governance clarity, risk architecture, and asset prioritization. Controls follow. Tooling enforces. Measurement sustains.
Security maturity is not defined by the number of policies in place or certificates on display. It is defined by whether the program reflects the organization’s actual risk landscape — and adapts as that landscape evolves.
That is the difference between appearing secure and being secure.
Follow us on Socials
Phone
info@securaconsults.com
+2348035333281
© 2026. Secura Consults Ltd. All rights Reserved.
